Satori Threat Intelligence Alert: Pushpaganda Manipulates Google Discovery Feeds with AI-Generated Content to Spread Malicious Notifications
Researchers: Louisa Abel, Vikas Parthasarathy, João Santos, Adam Sell
IVT Taxonomy: Automated Browsing, Misleading User Interface
HUMAN’s Satori Threat Intelligence and Research Team has identified a novel ad fraud, social engineering, and scareware threat dubbed Pushpaganda. This operation, named for push notifications central to the scheme, generates invalid organic traffic from real mobile devices by tricking users into subscribing to enabling notifications that presented alarming messages.
Pushpaganda’s primary mechanism for luring unsuspecting users is through Google’s Discovery feeds, the collection of news stories that appear on many Google properties. The threat actors use advanced SEO techniques and AI-generated content to inject deceptive news stories into the personalized content streams of Android and Chrome users. Once a user is lured to an actor-controlled domain, they are manipulated into enabling push notifications that later deliver scareware, fake legal threats, and financial scams.
At its peak, HUMAN observed roughly 240 million bid requests associated with Pushpaganda domains in a single 7-day period. While the operation initially targeted users in India, researchers have confirmed that the threat has expanded to impact users in Australia, the United States, and beyond. Researchers shared the full list of 113 Pushpaganda-associated domains with Google, and Google confirmed a fix has been deployed to prevent low quality, manipulative content like the content generated by the Pushpaganda operation from appearing in users’ Discovery feeds.
Customers partnering with HUMAN for Ad Fraud Defense and Ad Click Defense are protected from Pushpaganda.
How Pushpaganda Worked
Pushpaganda is, at the highest level, a case of social engineering:
- Threat actors created a collection of 113 domains and used AI to generate sensationalist and misleading articles and images that would appeal to users at a glance.
- These articles were inserted, via either SEO or paid placement, into users’ Discovery feeds on various Google properties, including blank browser tabs, inviting users to click through to the domain to read more.
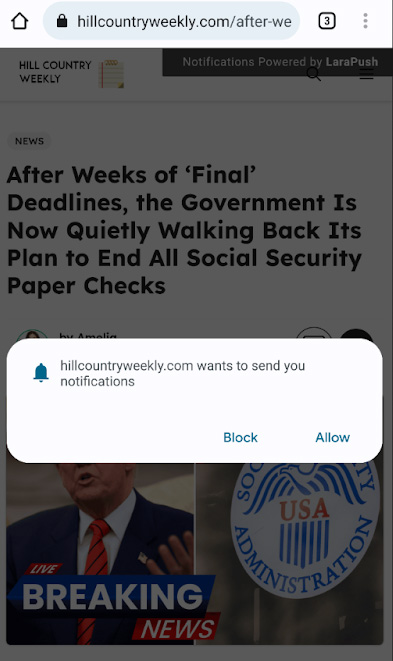
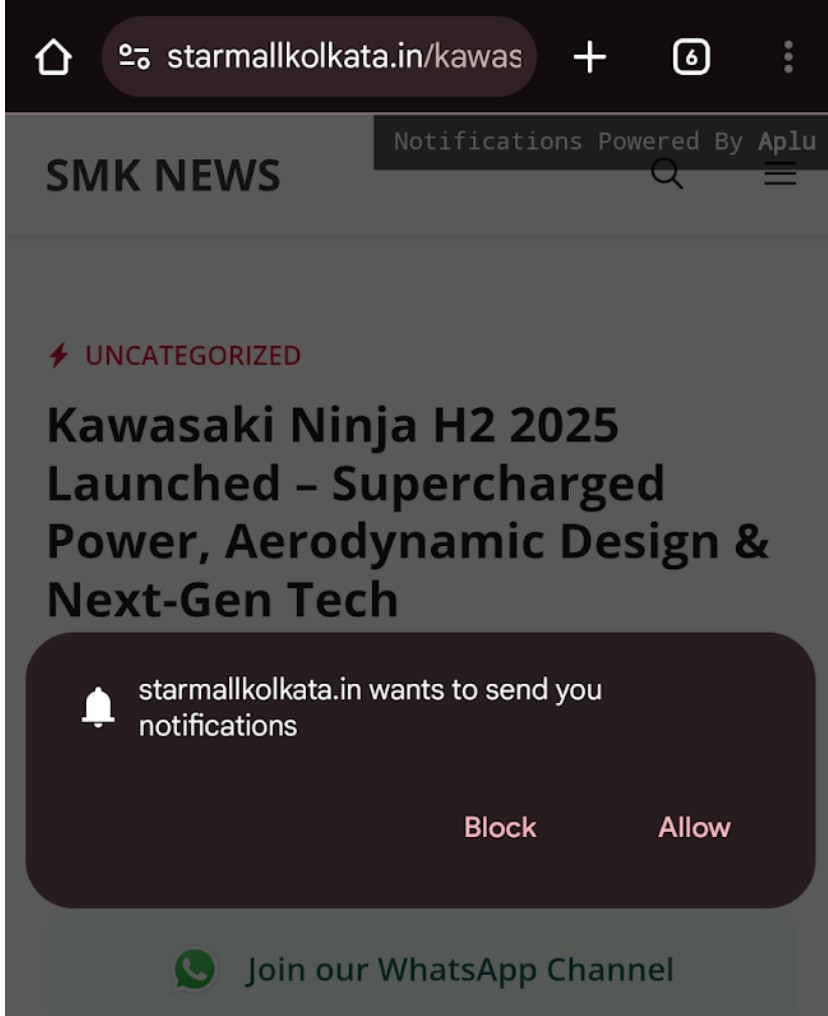
- On visiting a Pushpaganda-associated domain, users are presented with the option to enable push notifications from the website.
- If the user agrees to allow these notifications, they’ll begin seeing a series of alarming and intimidating notifications bearing no relationship to the domain from which they were enabled.
- Clicking through from one of the push notifications lands a user on another Pushpaganda-associated domain.
- Some Pushpaganda-associated domains further exploit users by presenting deceptive buttons which launch new active browser tabs while rotating inactive browser tabs among Pushpaganda-associated domains, requesting and rendering ads. This results in additional ad loads and makes the domains appear to be higher-value to advertisers.
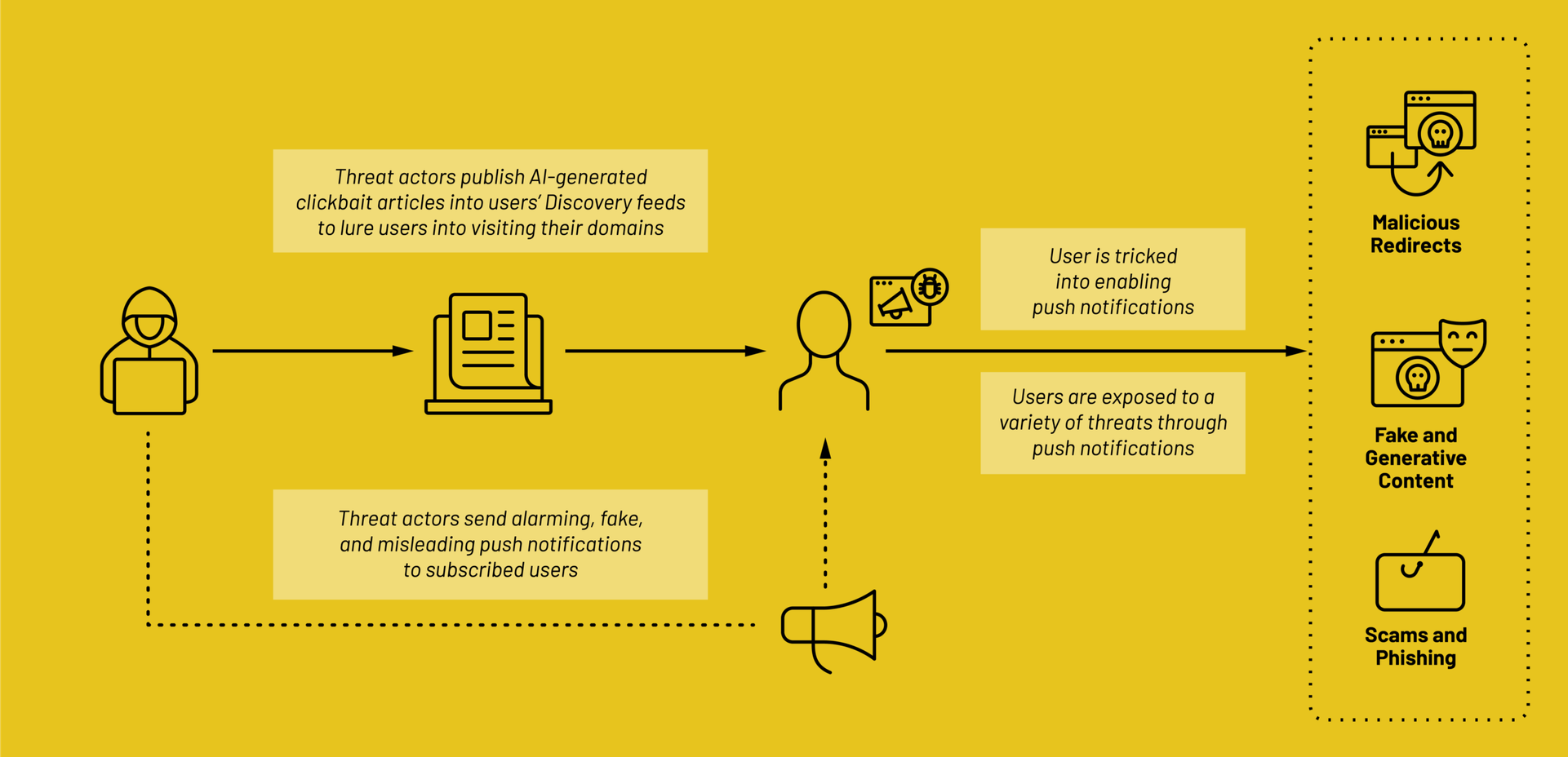
Ad impressions and clicks occurring as a result of this social engineering are considered invalid because they don’t reflect true user intent.
Manipulating the Discovery Feed
One of the most novel components of Pushpaganda is the use of Google’s Discovery feed as a proliferation tactic. The feed is a personalized news stream found on Android home screens and blank Chrome tabs, and as such has high user exposure. Researchers are unsure if Pushpaganda-related content showing in users’ Discovery feeds is purchased by the threat actors or if there are advanced SEO techniques at play. Regardless of the means by which the content appears, however, the strategy has been effective at exposing the content to users.
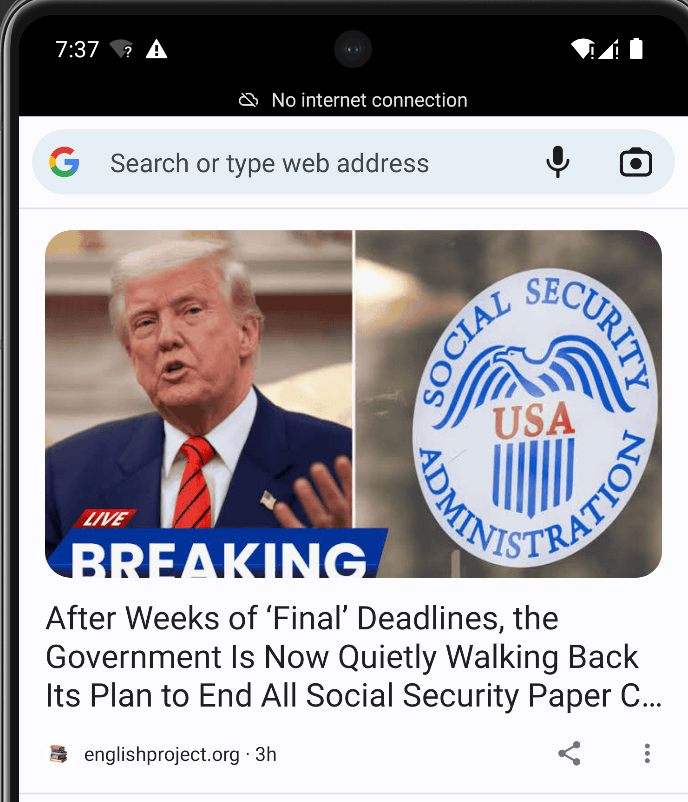
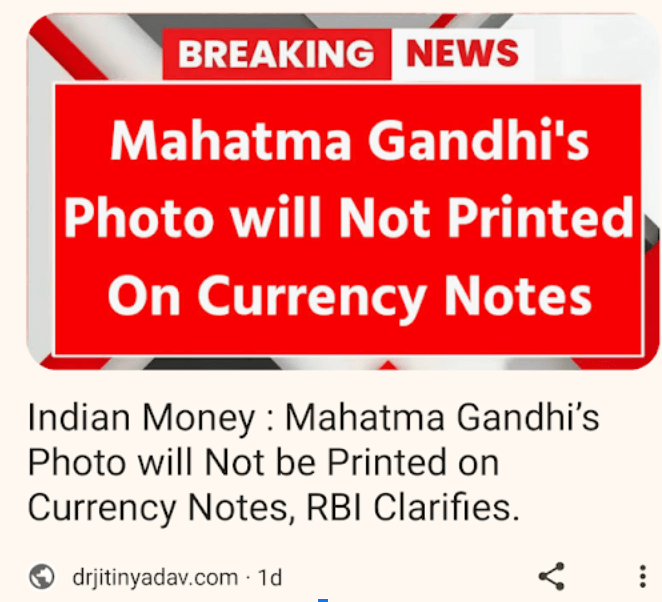
Many of the articles’ headlines and images show hallmarks of being AI-generated, and frequently fall within one of a few categories intended to drive high engagement:
- Financial/Political Lures: Articles focusing on taxes, currency updates, or government direct deposits (e.g., “$1390 IRS Deposit Approved”).
- Sensationalist Tech Claims: Unrealistic stories about $100 smartphones with 300MP+ cameras.
Malicious Push Notification Cycles
Once a user clicks a Discovery feed link, they are redirected to a Pushpaganda-associated domain where a notification subscription prompt is immediately triggered. Users often click “Allow” to bypass the alert or access the promised content.
Once subscribed, the browser allows the site to push persistent notifications directly to the user’s OS level, bypassing traditional ad blockers.
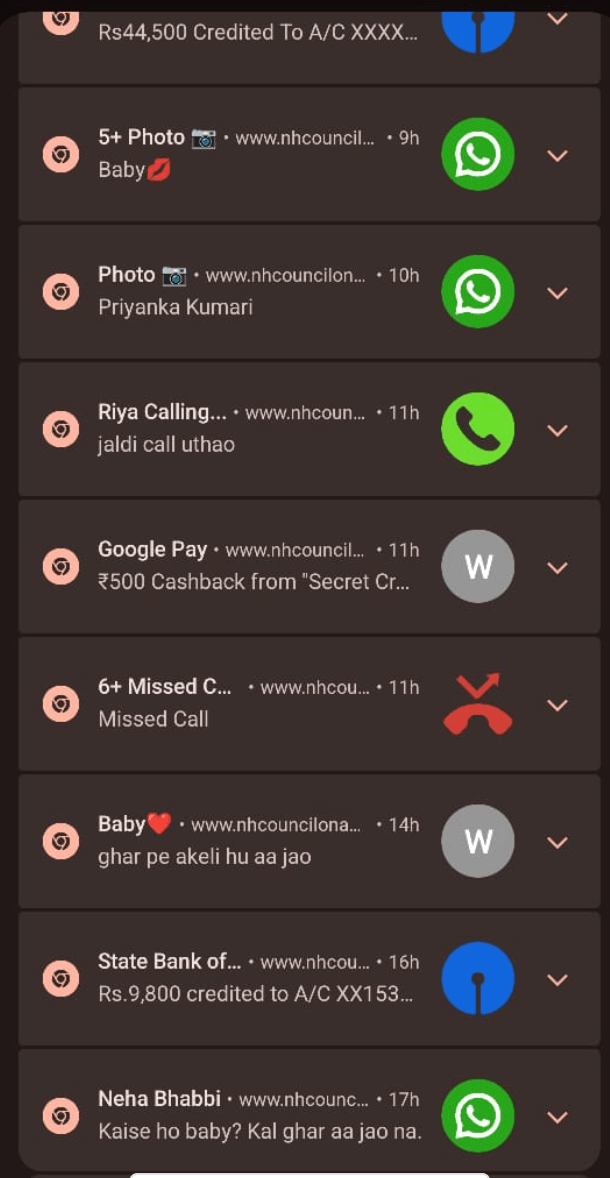
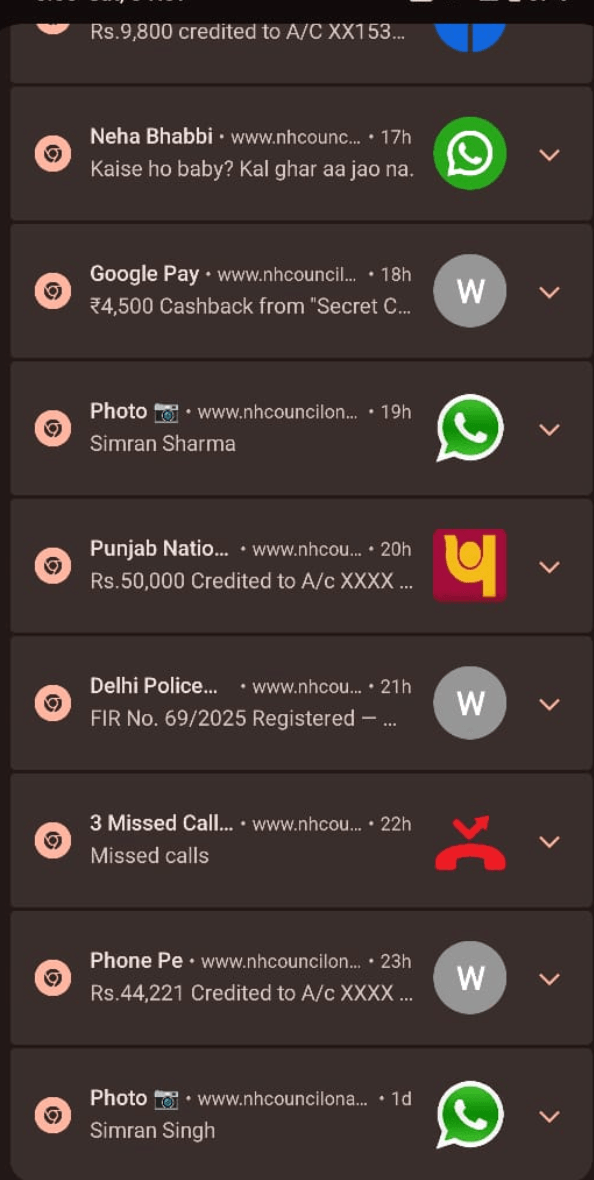
Researchers observed heavy use of psychological manipulation (scareware) to entice clicks of push notifications:
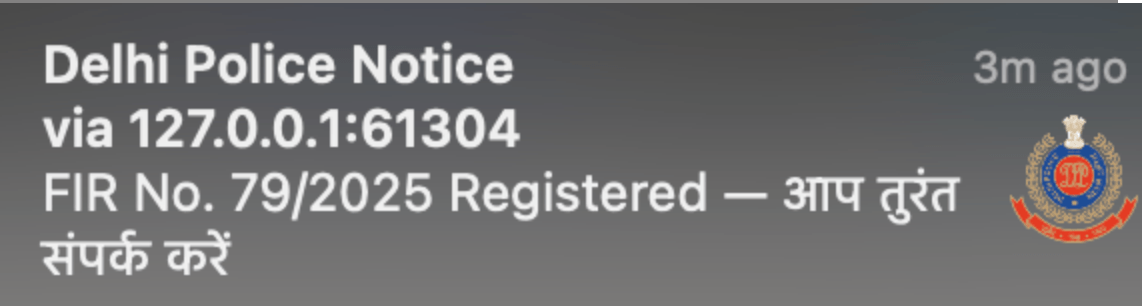
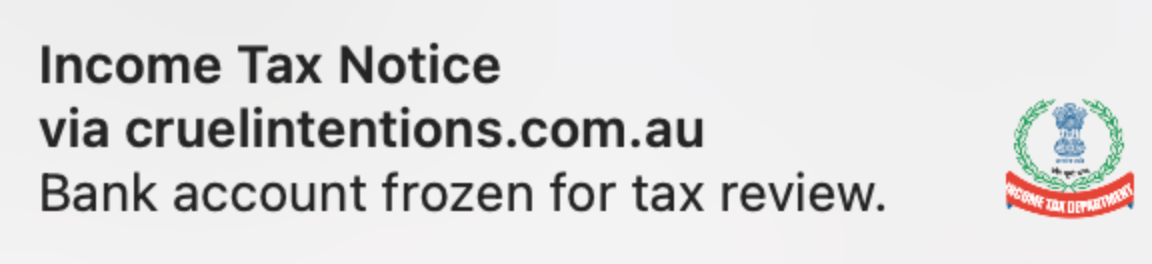
- Legal Threats: Fake arrest warrants or police notices.
- Social Engineering: Mimicked missed calls from “Mom” or other family members.
- Financial Alerts: False bank deposits or tax review notices.
Notice above that the icons attached to the notifications do not correspond to the domains from which the notification was sent.
Clicking a Pushpaganda-associated push notification directs the user to a new actor-controlled domain, often creating a cycle where each new site urges the user to subscribe to further notifications.
Deceptive UI and JavaScript Rotation
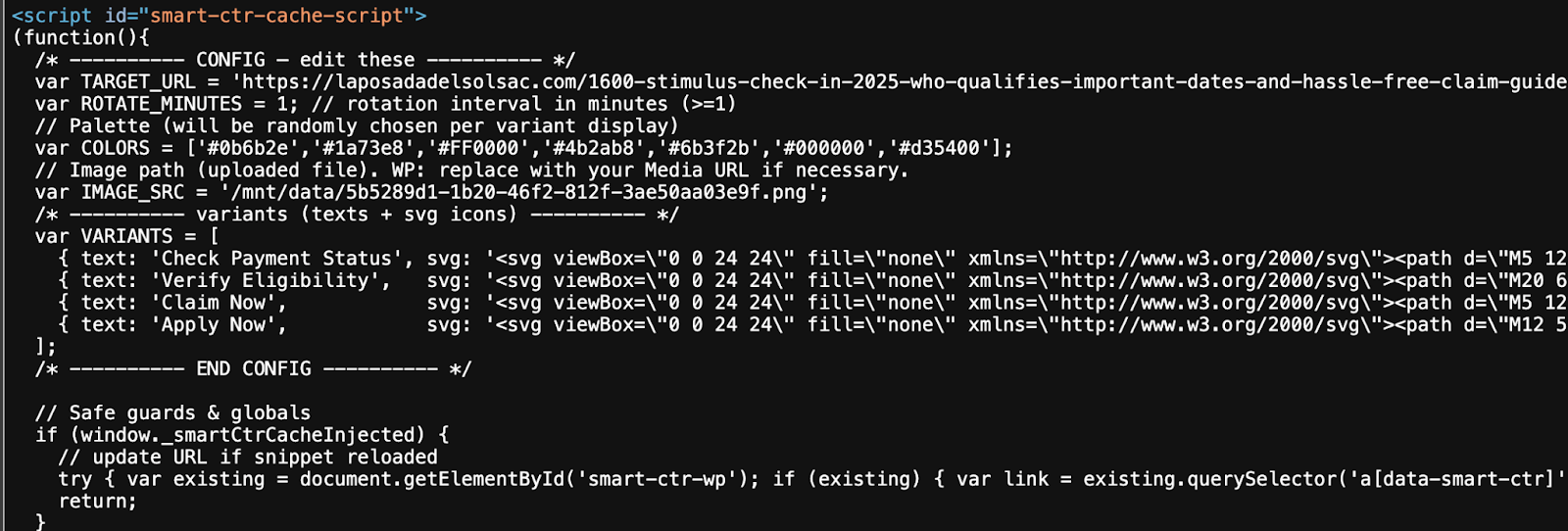
To further inflate engagement metrics and page views, some Pushpaganda domains employ deceptive buttons, with labels such as “Apply Now,” “Claim Now,” or “Join WhatsApp.”
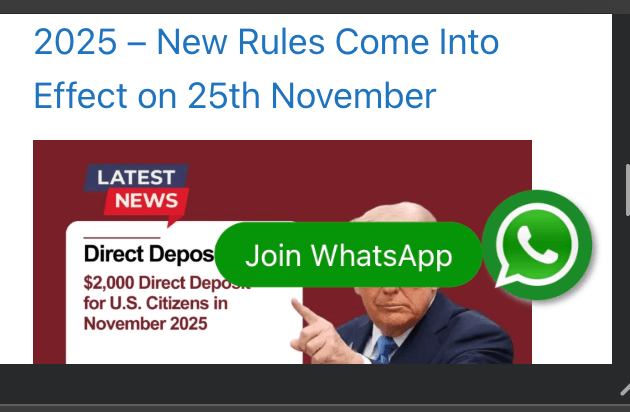
Rather than fulfilling these actions, the buttons use JavaScript to redirect users to additional internal articles or different actor-controlled domains.
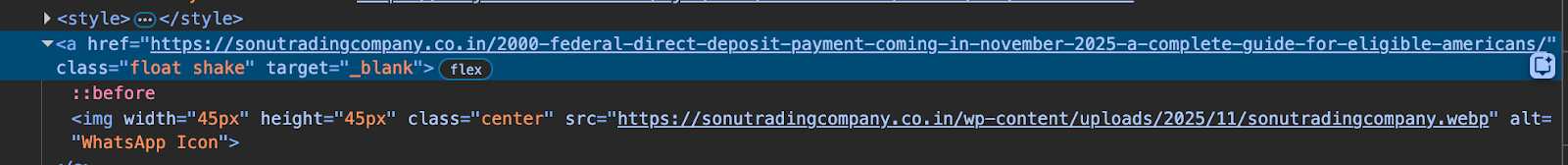
The buttons themselves are the result of a piece of JavaScript that changes the text, color, and how frequently the button refreshes:
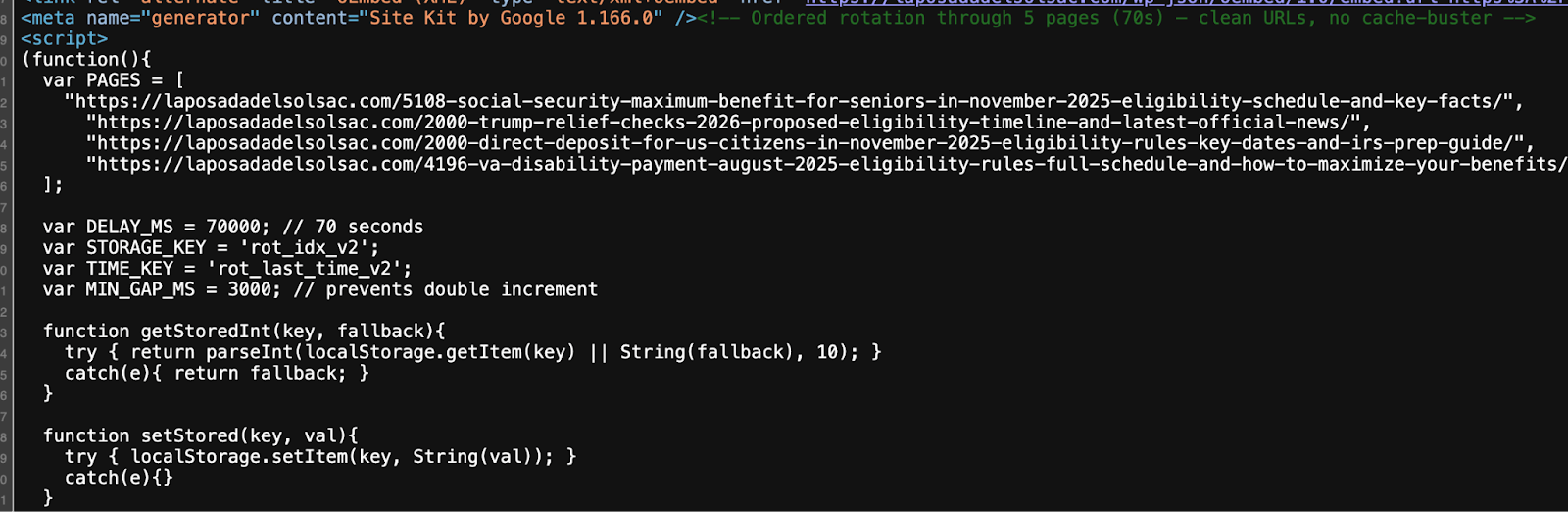
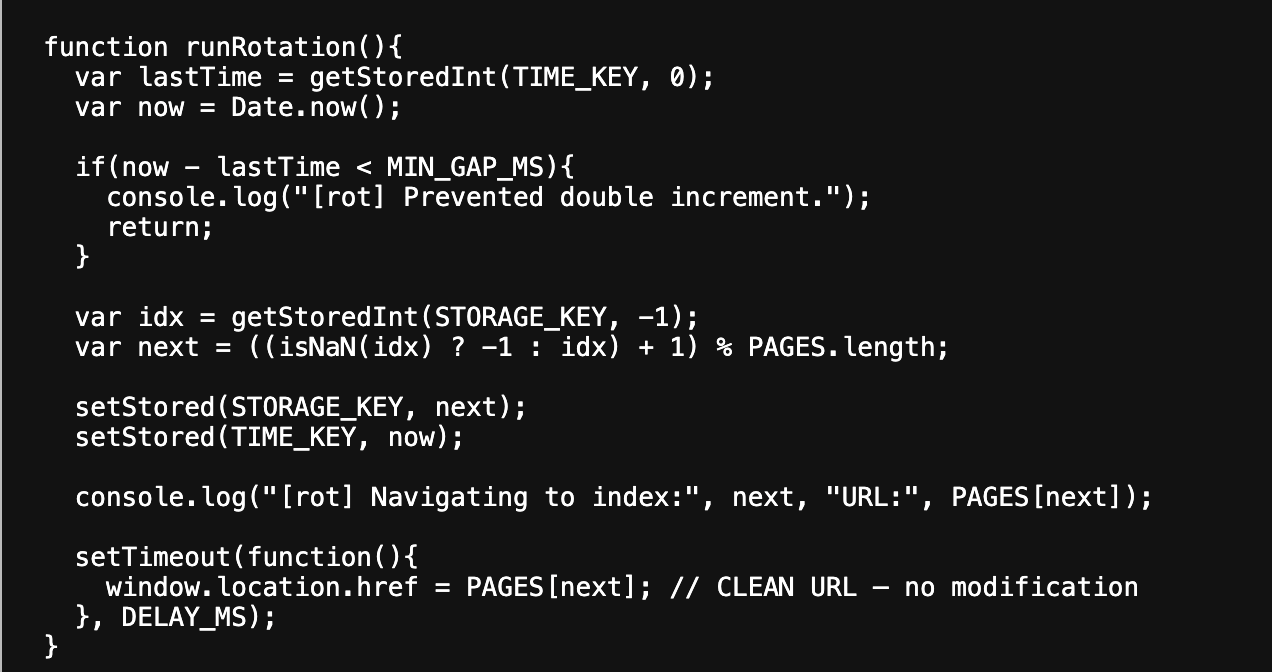
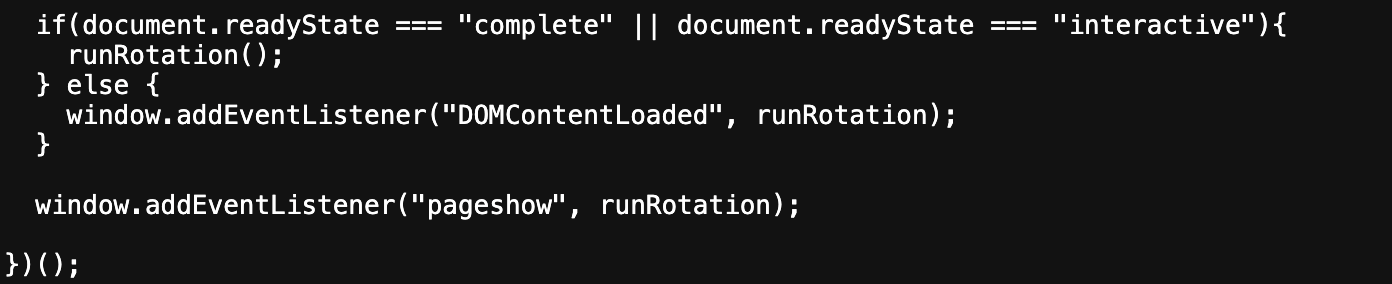
A target=”_blank” attribute in the HTML of the button instructs the browser to open the URL in a new tab. In the existing tab, however, a new component of the scheme begins.
Satori researchers identified a JavaScript rotation algorithm that forces inactive tabs or background windows to automatically cycle through various actor-owned pages. This mechanism results in additional ad loads and increased session durations, making the sites appear high-quality to ad networks.
Deepfake Ads
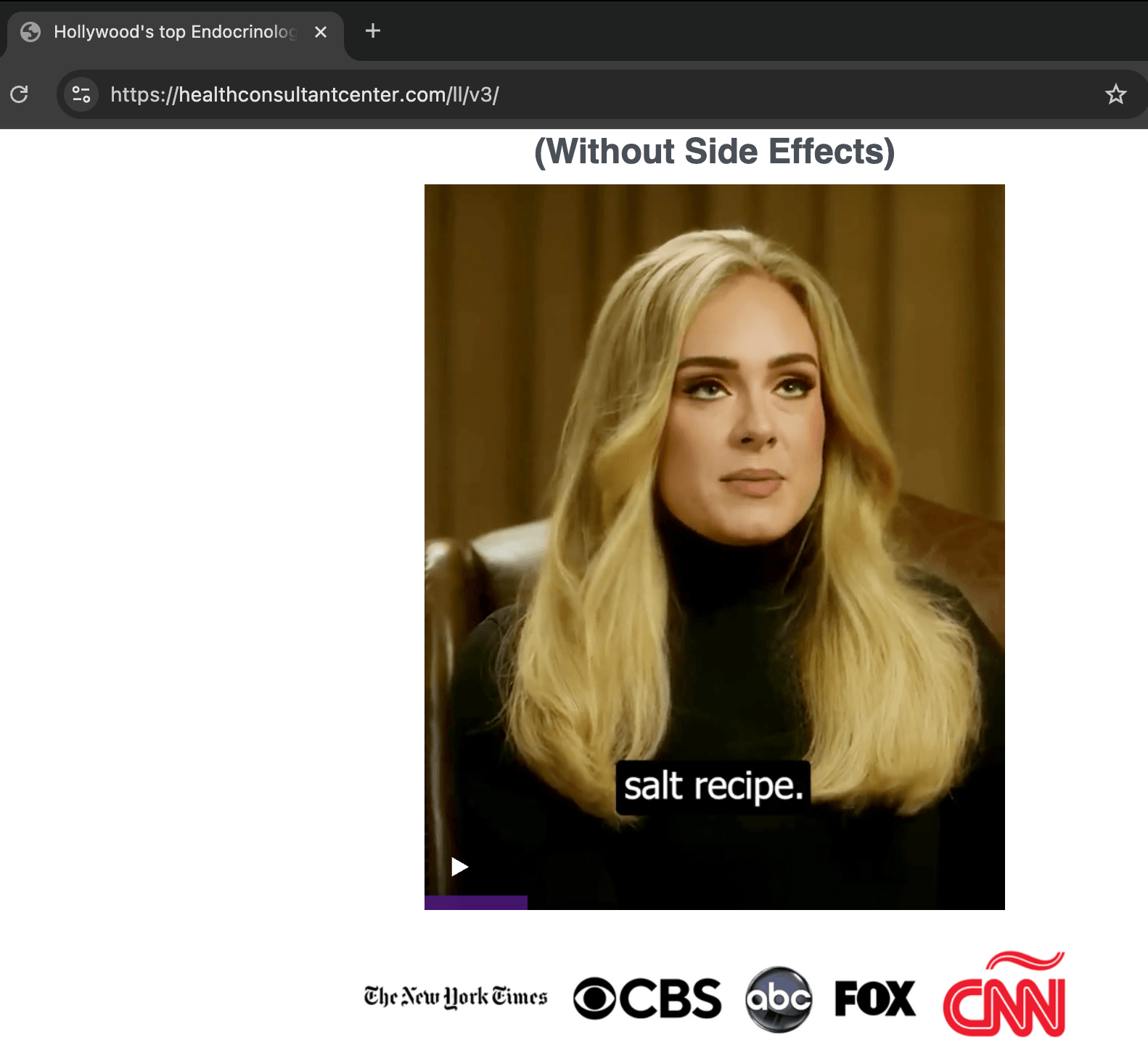
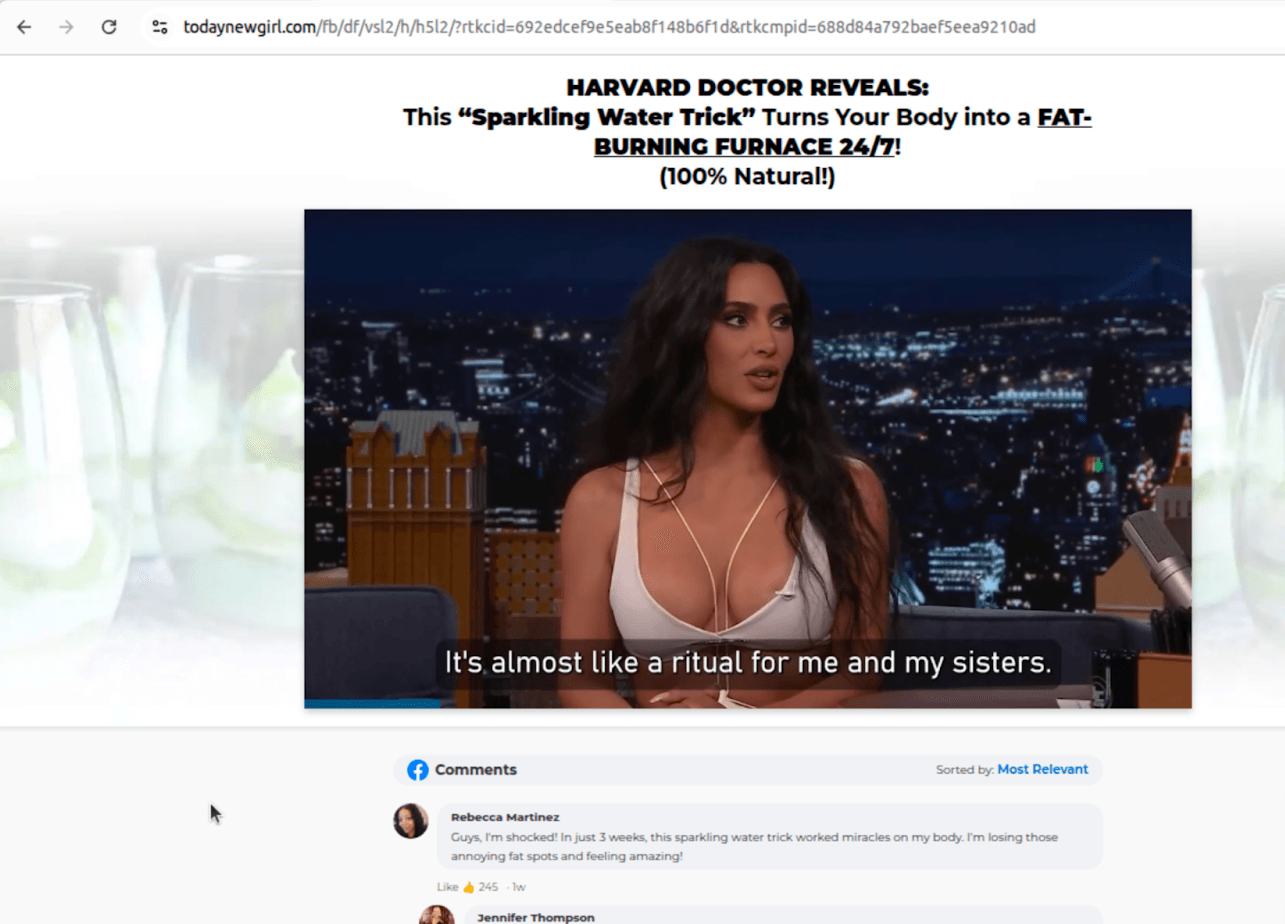
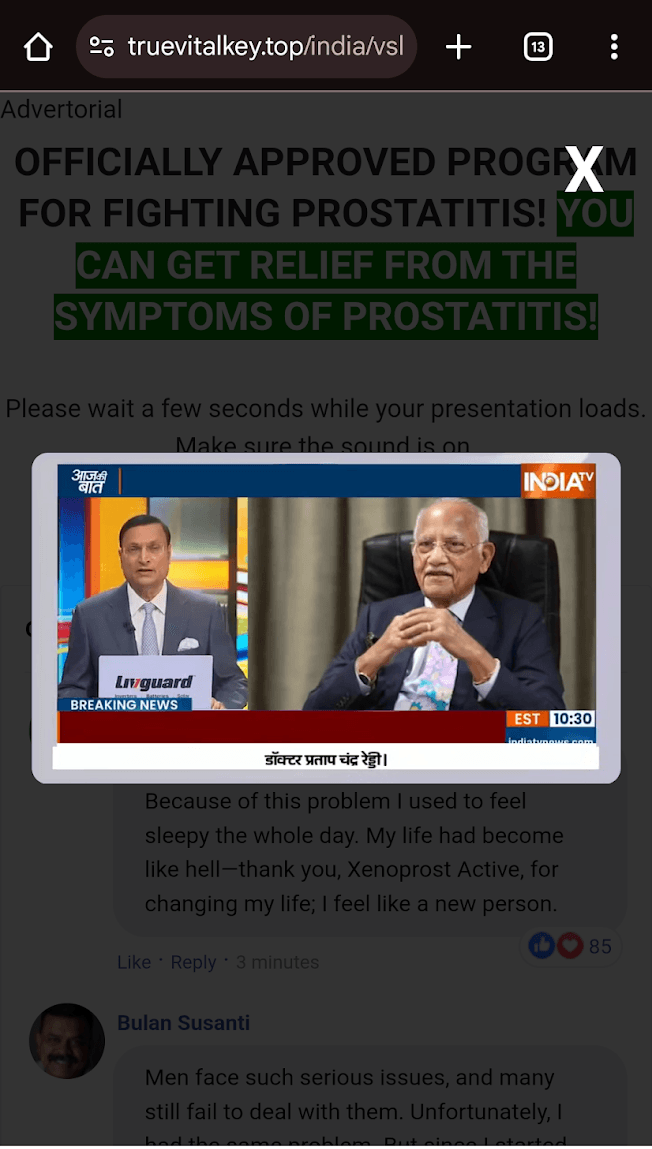
Finally, Satori researchers have observed the use of deepfake content included in ads on Pushpaganda-associated domains:
Some observed deepfakes reference celebrities or medical professionals:
These fake endorsements allow the threat actors to exploit user trust at scale. Satori researchers found the threat actors behind these deepfake images and videos also placing ads with this content on other domains and through other channels.
Protecting the Ecosystem
Because the Discovery Feed is a system capability rather than a standalone app, mitigation focuses on blocking the underlying infrastructure:
- Ad Fraud Defense/Ad Click Defense: Bid requests and clicks connected to Pushpaganda-related domains are flagged as invalid.
- Continuous Monitoring: Satori continues to track the emergence of new Pushpaganda domains and for the possibility of threat actor adaptation.
Customers partnering with HUMAN for Ad Fraud Defense and Ad Click Defense are protected from the impacts of the Pushpaganda operation. Users can block malicious push notifications by following these instructions for each domain.
As threat actors increasingly incorporate AI into their attack tactics, HUMAN remains committed to disrupting their monetization cycles at the source.