Key Capabilities
Detect and block bots that skew engagement metrics to protect data integrity and support smarter decision-making.

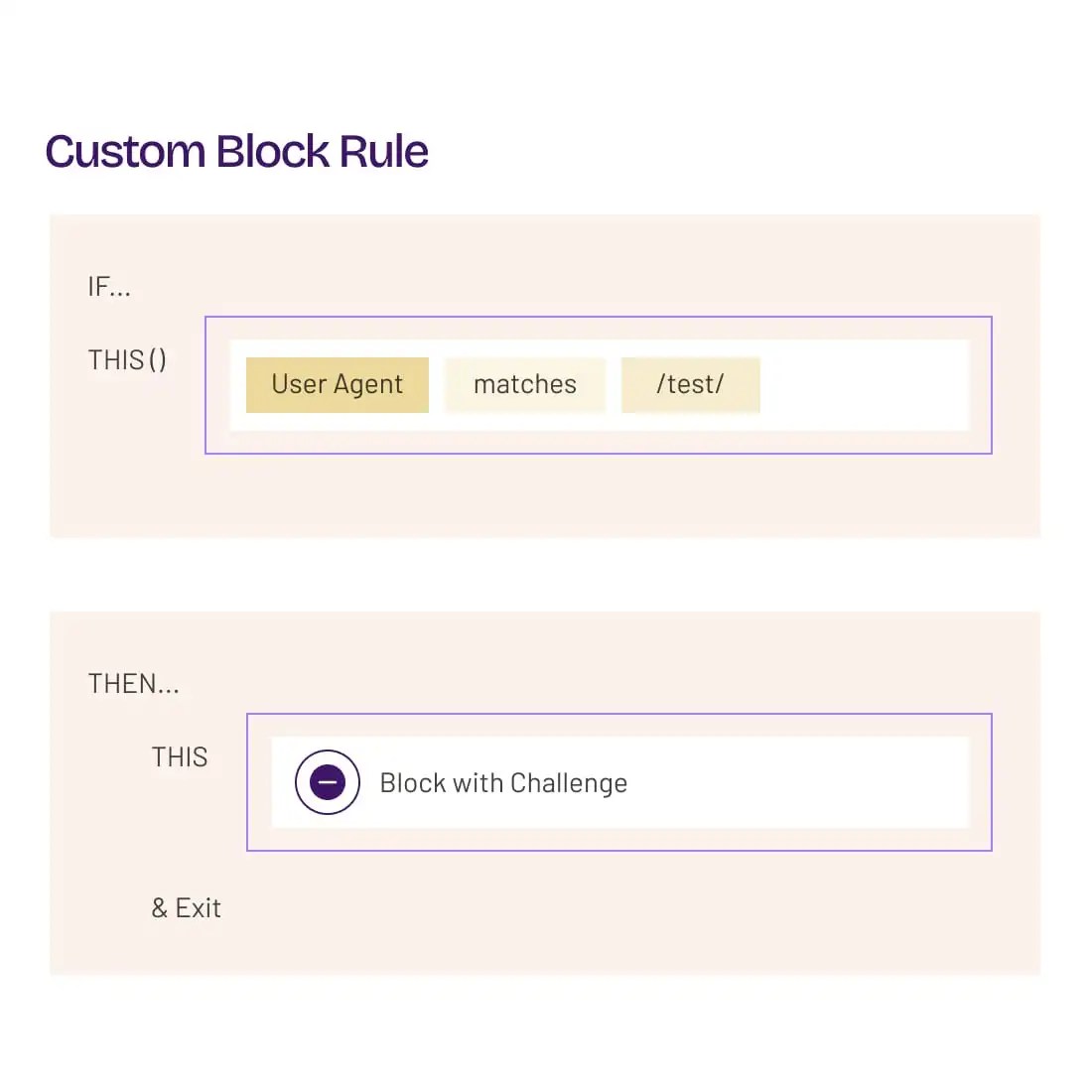
Frictionless Verification Challenges
Block bots at the edge without adding friction for real users with scenario-optimized, customizable verification challenges, Precheck and Human Challenge.
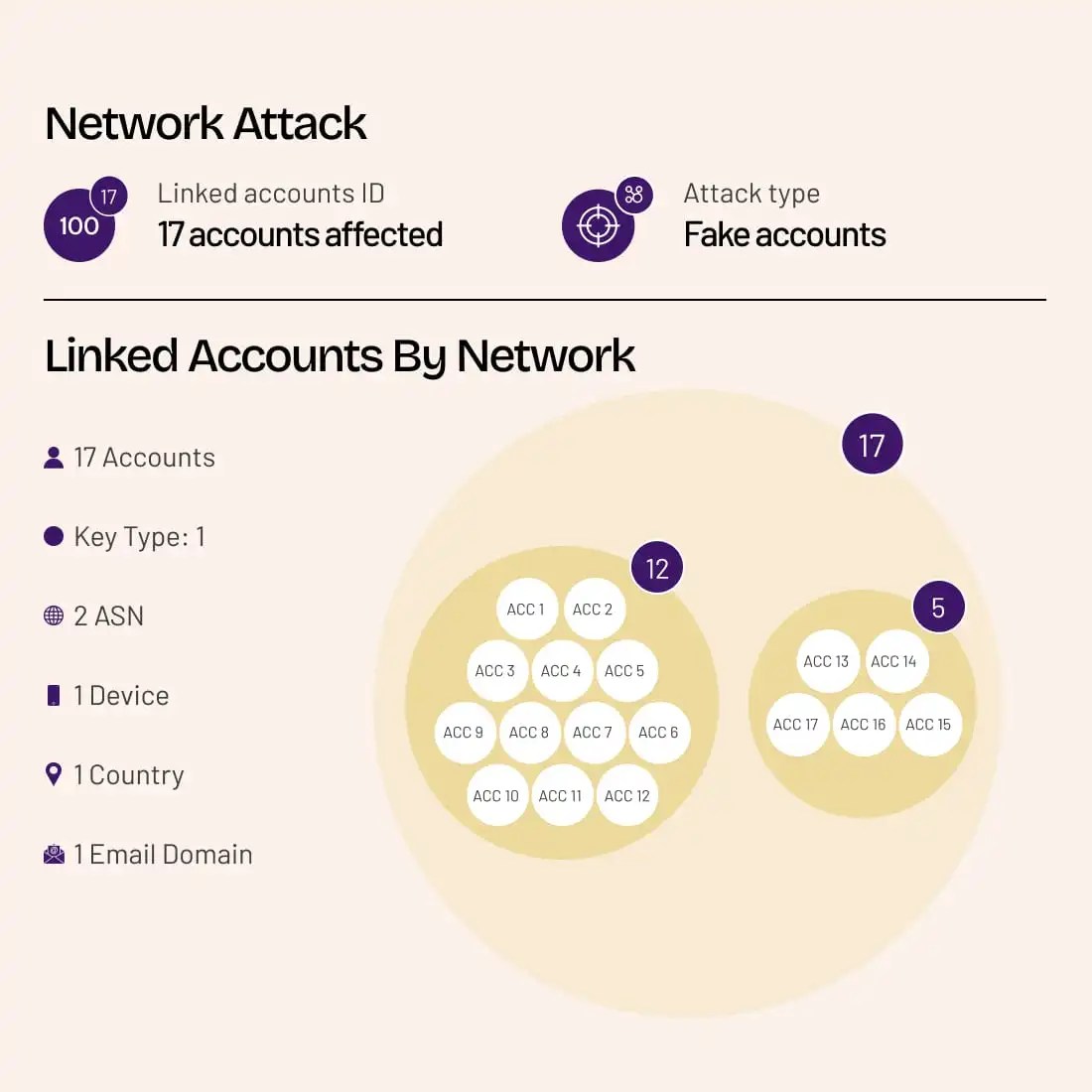
Block Fake Account Interactions
Detect and mitigate fake accounts that are being used to fraudulently interact with your application. Uncover and neutralize fraud networks.
Filter Out Bots that Skew Analytics
Choose how to respond to bot traffic with a range of response actions, including hard blocking, soft mitigation, honey pots, and serving deceptive content.
Protecting Customers from Evolving Risks
HUMAN is trusted by global organizations across industries to protect against data contamination and skewed analytics due to bot traffic.
Threat Intelligence:
The HUMAN Element
The Satori Threat Intelligence and Research Team uncovers, analyzes, and disrupts cyberthreats and fraud schemes that undermine trust across the digital landscape, delivering cutting-edge research that strengthens protection for customers and thwarts bad actors for a safer internet.
Explore Satori
Secure Your Data with HUMAN
Detect and mitigate sophisticated bot traffic that contaminates your data and skews web analytics with HUMAN Sightline.
Learn More
FAQ
How does contaminated data affect campaigns?
Contaminated data undermines the accuracy of campaign performance measurements. When bots or other invalid traffic inflate metrics like engagement rates, conversion volume, or audience reach, marketers may believe a campaign is more effective than it actually is. This misrepresentation can lead to misallocated budgets, flawed A/B testing results, and ineffective retargeting strategies. Long term, it erodes trust in analytics platforms and makes it difficult to optimize for real human audiences.
What are skewed analytics?
Skewed analytics occur when data collected from digital channels is distorted or inaccurate, often due to the presence of invalid traffic such as bots, click farms, or non-human interactions. This contamination leads to misleading insights, where performance metrics like impressions, clicks, or conversions no longer reflect true user behavior. As a result, businesses may make strategic decisions based on faulty assumptions, wasting resources and missing real opportunities for optimization.
Can HUMAN prevent skewed analytics?
Yes. HUMAN prevents skewed analytics by filtering out invalid traffic. Using advanced machine learning, behavioral signals, and device fingerprinting, HUMAN detects and blocks bots and other automated threats in real time. By ensuring genuine human interactions are measured, HUMAN helps marketing and analytics teams maintain clean, actionable data that reflects true campaign performance.
How does HUMAN manage invalid traffic?
HUMAN manages invalid traffic through a layered detection and mitigation system that combines behavioral analysis, threat intelligence, and continuous machine learning. It examines signals like navigation patterns, interaction speed, and device anomalies to determine whether traffic is human or not. Bot traffic is flagged or blocked in real time, and insights are delivered through detailed reporting dashboards. This approach helps businesses protect their ad spend, improve campaign efficiency, and maintain the integrity of their data across channels.
What types of bot traffic can HUMAN block?
HUMAN blocks a wide range of malicious bot traffic, including malvertising, account takeover attempts, scraping, ad fraud, and inventory hoarding. Our solutions go beyond basic detection, using behavioral analysis, device fingerprinting, and real-time threat intelligence to ensure that only legitimate users interact with your digital properties. This layered protection helps businesses stop sophisticated bots before they cause financial, operational, or reputational damage.
Request a Demo